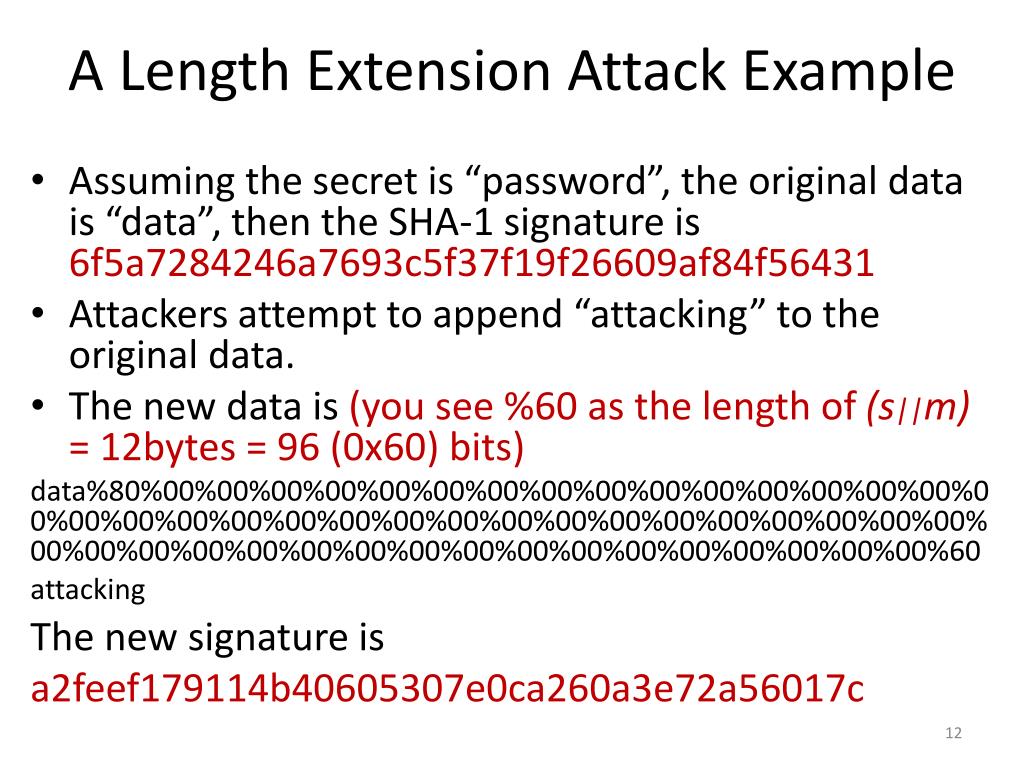
Length Extension Attack Ctf Writeup . so, a length extension attack is a type of attack where an attacker can use hash (message1) and the length of. I'll detail below what i've understood so. Generate a md5 of 64 as. the objective of this lab is to help students understand how the length extension attack works. a length extension attack is a sophisticated cryptographic exploit that targets hash functions, taking advantage. if an attacker wants to append the string append he can: Students will launch the attack. Change the state of the previously.
from www.slideserve.com
I'll detail below what i've understood so. so, a length extension attack is a type of attack where an attacker can use hash (message1) and the length of. if an attacker wants to append the string append he can: the objective of this lab is to help students understand how the length extension attack works. Generate a md5 of 64 as. Change the state of the previously. Students will launch the attack. a length extension attack is a sophisticated cryptographic exploit that targets hash functions, taking advantage.
PPT 2 Length Extension Attack PowerPoint Presentation, free
Length Extension Attack Ctf Writeup Generate a md5 of 64 as. if an attacker wants to append the string append he can: Change the state of the previously. Students will launch the attack. a length extension attack is a sophisticated cryptographic exploit that targets hash functions, taking advantage. Generate a md5 of 64 as. I'll detail below what i've understood so. so, a length extension attack is a type of attack where an attacker can use hash (message1) and the length of. the objective of this lab is to help students understand how the length extension attack works.
From www.slideserve.com
PPT 2 Length Extension Attack PowerPoint Presentation, free Length Extension Attack Ctf Writeup I'll detail below what i've understood so. Students will launch the attack. a length extension attack is a sophisticated cryptographic exploit that targets hash functions, taking advantage. Generate a md5 of 64 as. so, a length extension attack is a type of attack where an attacker can use hash (message1) and the length of. if an attacker. Length Extension Attack Ctf Writeup.
From www.youtube.com
Length Extension Attack YouTube Length Extension Attack Ctf Writeup if an attacker wants to append the string append he can: the objective of this lab is to help students understand how the length extension attack works. so, a length extension attack is a type of attack where an attacker can use hash (message1) and the length of. a length extension attack is a sophisticated cryptographic. Length Extension Attack Ctf Writeup.
From conmagor.com
Diseccionando el SHA512, un preludio al Length Extension Attack. Length Extension Attack Ctf Writeup Change the state of the previously. Generate a md5 of 64 as. a length extension attack is a sophisticated cryptographic exploit that targets hash functions, taking advantage. so, a length extension attack is a type of attack where an attacker can use hash (message1) and the length of. I'll detail below what i've understood so. Students will launch. Length Extension Attack Ctf Writeup.
From ciphersaw.me
Hash Length Extension Attack(哈希长度扩展攻击) Secrypt Agency Length Extension Attack Ctf Writeup Change the state of the previously. if an attacker wants to append the string append he can: a length extension attack is a sophisticated cryptographic exploit that targets hash functions, taking advantage. the objective of this lab is to help students understand how the length extension attack works. I'll detail below what i've understood so. Generate a. Length Extension Attack Ctf Writeup.
From www.youtube.com
SHA1 length extension attack on the Secure Filesystem rhme2 Secure Length Extension Attack Ctf Writeup Generate a md5 of 64 as. a length extension attack is a sophisticated cryptographic exploit that targets hash functions, taking advantage. so, a length extension attack is a type of attack where an attacker can use hash (message1) and the length of. Change the state of the previously. the objective of this lab is to help students. Length Extension Attack Ctf Writeup.
From medium.com
The Partial Preimage Technique. How to Use Length Extension Attacks For Length Extension Attack Ctf Writeup I'll detail below what i've understood so. Generate a md5 of 64 as. the objective of this lab is to help students understand how the length extension attack works. a length extension attack is a sophisticated cryptographic exploit that targets hash functions, taking advantage. so, a length extension attack is a type of attack where an attacker. Length Extension Attack Ctf Writeup.
From ciphersaw.me
Hash Length Extension Attack(哈希长度扩展攻击) Secrypt Agency Length Extension Attack Ctf Writeup if an attacker wants to append the string append he can: Students will launch the attack. a length extension attack is a sophisticated cryptographic exploit that targets hash functions, taking advantage. I'll detail below what i've understood so. the objective of this lab is to help students understand how the length extension attack works. Change the state. Length Extension Attack Ctf Writeup.
From studylib.net
Hash Length Extension Attacks Explained Length Extension Attack Ctf Writeup if an attacker wants to append the string append he can: a length extension attack is a sophisticated cryptographic exploit that targets hash functions, taking advantage. so, a length extension attack is a type of attack where an attacker can use hash (message1) and the length of. Students will launch the attack. Generate a md5 of 64. Length Extension Attack Ctf Writeup.
From blog.csdn.net
Length Extension Attack_length extension attack对sha256有用吗CSDN博客 Length Extension Attack Ctf Writeup I'll detail below what i've understood so. a length extension attack is a sophisticated cryptographic exploit that targets hash functions, taking advantage. Change the state of the previously. the objective of this lab is to help students understand how the length extension attack works. if an attacker wants to append the string append he can: Students will. Length Extension Attack Ctf Writeup.
From www.slideserve.com
PPT 2 Length Extension Attack PowerPoint Presentation, free Length Extension Attack Ctf Writeup the objective of this lab is to help students understand how the length extension attack works. a length extension attack is a sophisticated cryptographic exploit that targets hash functions, taking advantage. Students will launch the attack. Generate a md5 of 64 as. I'll detail below what i've understood so. if an attacker wants to append the string. Length Extension Attack Ctf Writeup.
From www.studocu.com
Hash Length Extension Attack Lab Lab 10 Hash length extension Length Extension Attack Ctf Writeup Generate a md5 of 64 as. the objective of this lab is to help students understand how the length extension attack works. a length extension attack is a sophisticated cryptographic exploit that targets hash functions, taking advantage. Change the state of the previously. so, a length extension attack is a type of attack where an attacker can. Length Extension Attack Ctf Writeup.
From www.slideserve.com
PPT 2 Length Extension Attack PowerPoint Presentation, free Length Extension Attack Ctf Writeup I'll detail below what i've understood so. Students will launch the attack. Generate a md5 of 64 as. Change the state of the previously. so, a length extension attack is a type of attack where an attacker can use hash (message1) and the length of. the objective of this lab is to help students understand how the length. Length Extension Attack Ctf Writeup.
From www.youtube.com
Length Extension Attack YouTube Length Extension Attack Ctf Writeup if an attacker wants to append the string append he can: Change the state of the previously. the objective of this lab is to help students understand how the length extension attack works. Students will launch the attack. so, a length extension attack is a type of attack where an attacker can use hash (message1) and the. Length Extension Attack Ctf Writeup.
From danq.me
Length Extension Attack Demonstration Dan Q Length Extension Attack Ctf Writeup if an attacker wants to append the string append he can: Students will launch the attack. Generate a md5 of 64 as. the objective of this lab is to help students understand how the length extension attack works. Change the state of the previously. a length extension attack is a sophisticated cryptographic exploit that targets hash functions,. Length Extension Attack Ctf Writeup.
From www.studocu.com
Crypto Hash Length Ext Hash Length Extension Attack Lab Copyright Length Extension Attack Ctf Writeup Students will launch the attack. the objective of this lab is to help students understand how the length extension attack works. I'll detail below what i've understood so. so, a length extension attack is a type of attack where an attacker can use hash (message1) and the length of. a length extension attack is a sophisticated cryptographic. Length Extension Attack Ctf Writeup.
From www.synopsys.com
a SHA1 MAC using a lengthextension attack in Python Synopsys Length Extension Attack Ctf Writeup I'll detail below what i've understood so. Generate a md5 of 64 as. Change the state of the previously. the objective of this lab is to help students understand how the length extension attack works. a length extension attack is a sophisticated cryptographic exploit that targets hash functions, taking advantage. so, a length extension attack is a. Length Extension Attack Ctf Writeup.
From www.slideserve.com
PPT Cryptography Crash Course PowerPoint Presentation, free download Length Extension Attack Ctf Writeup so, a length extension attack is a type of attack where an attacker can use hash (message1) and the length of. a length extension attack is a sophisticated cryptographic exploit that targets hash functions, taking advantage. Change the state of the previously. the objective of this lab is to help students understand how the length extension attack. Length Extension Attack Ctf Writeup.
From github.com
GitHub Wen1i/Project03lengthextensionattack md5,sha256,sm3的长度扩展攻击 Length Extension Attack Ctf Writeup Students will launch the attack. if an attacker wants to append the string append he can: I'll detail below what i've understood so. Generate a md5 of 64 as. a length extension attack is a sophisticated cryptographic exploit that targets hash functions, taking advantage. Change the state of the previously. so, a length extension attack is a. Length Extension Attack Ctf Writeup.